You'd probably agree that phishing attack emails are getting ridiculously hard to spot. They can cause massive harm when they do hit and the fear of them can be truly paralysing for any organisation. You may even have been hit by such an attack yourself.
Funnily enough I received what appeared to be just such an attack, shown below, in the early hours of last Saturday morning. This was after I'd been on a spending spree using my credit card the night before.
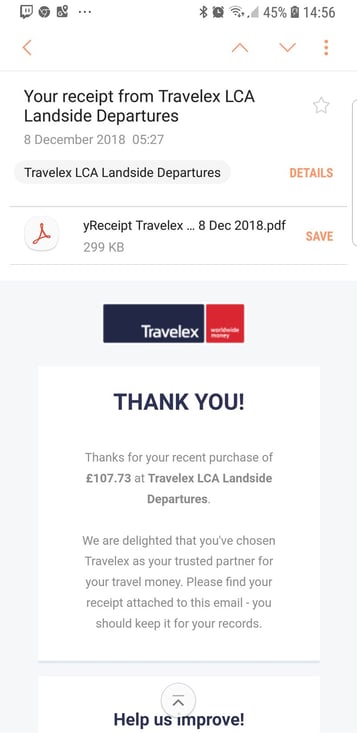
Everything on this email certainly looks legitimate to me and I'm sure you'd agree; the English is good, the layout looks right, even when you click to see the contact it is in a format that looks completely spot-on, even to a self-professed expert.
However even after a couple of shameless pints the night before, I'm 100% sure I did not buy travel money - particularly as Tatton Park is probably the most exotic place I'm lucky enough to be travelling to over the next couple of months.
So, that leaves me with a real dilemma. I've either been the victim of credit card fraud (which has happened to me before, very annoying, and incredibly hard to protect yourself against) OR this is a perfect example of phishing attack emails in the wild.
How do I move forward?
You can be sure as hell I'm not clicking on the PDF to open it on my personal phone, which has no protection outside of what comes standard (perhaps silly, but a mistake I'm sure something a lot of people are guilty of).
Equally I'm not sending it to any corporate device which have said filters either, I’m not that daft, particularly in the wake of growing supply chain attacks.
So here I am, phone in hand, left completely in a state of relative paralysis. It seems the best course of action is to do absolutely nothing - do nothing and hope that nothing worse happens. The 'Ostrich approach', if you will. Not a great state of affairs and it certainly isn't one that sits well with me.
So this got me to thinking: I am just one person, with one device, on one connection. I am certainly not going to be held to any sort of regulation if something nasty does transpire from this (I hope!), I’m not facing any fines and apart from being a tad annoyed and suffering some mild embarrassment. I’m not going to “lose face” over it.
The same cannot be said for companies where the polar opposite of the above sentence holds true. The fines are very real, the loss of face can cost companies a fortune, and if nothing else a bad breach will quite often mean one or more people looking for a new job.
And mobiles, as in my case, are just one area being targeted.
So, how do I manage phishing attack emails?
My point to you is three-fold.
Firstly, I get it, these attacks now are not the lame Nigerian prince attacks that they once were; easy to spot, easy to ignore and even somewhat amusing in some cases. They are clever, targeted and quite frankly a tad scary.
Secondly, pay attention to actually protecting your mobile estate! It’s the biggest growing platform in connectivity and honestly, just relying on either the baked in protection from the devices, or hoping that your MDM platform will pick up anything nefarious could really leave you with a hole in your defences that comes back to bite you.
Finally, If you or your business have suffered something similar, or are just concerned about the harrowing industry growth figures around phishing attack emails - let's connect and share out tale of woe together - The good news for me is that Intercity Technology has the capacity to stop such attacks in their wake without relying purely on my intuition. And even better - I'd love to share with you how they do it.
Subscribe to our newsletter
YOU MAY ALSO BE INTERESTED IN:


