IoT, BYOD and an always-on workforce are making the IT infrastructure more exposed to cyber attacks. See if your business is ready to face these threats with the Aruba | Intercity what's on your network Infographic below...
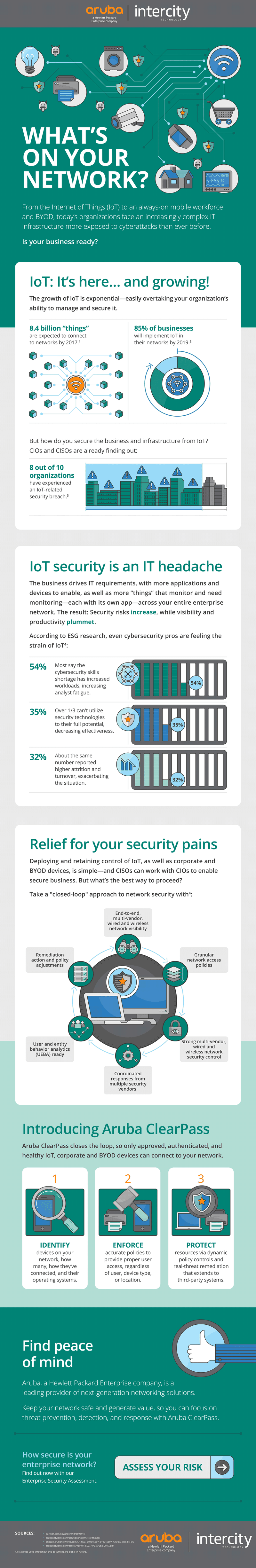
Still not sure if your business is ready to face the threats from IoT and BYOD? Find out more with our Enterprise Security Assessment here and discover just how secure your network truly is.
Subscribe to our newsletter
YOU MAY ALSO BE INTERESTED IN:
Intercity & GBCC Roundtable with Penny Mordaunt: Empowering Midlands Businesses
Last week we teamed up with the Greater Birmingham Chambers of Commerce to host a thought-provoking..
The Reality of Retail Price Index Increases...
In today's dynamic economic landscape, staying ahead of price increases and ensuring cost stability..
Navigating the Evolving Utilities Landscape
The B2B utilities landscape is experiencing shift, driven by changing customer needs and the quest..


